Colt SSE, powered by zscaler
With users, data, and applications across multiple locations and cloud environments, you need a modern security approach with security policies and risk management applied everywhere. That's where Colt Secure Service Edge (SSE) comes in.
































Benefits that empower progress





Related Insights
Why colt?
We deliver the extraordinary every day for our customers, people and partners. Here’s what sets us apart.
(Net Promoter Score)
Customer experience has always set us apart and our NPS score is one of the best in the industry.

Buildings connected
With Colt fibre and millions more available via our Colt Network as a Service platform across Europe, Asia and the US.
Data Centres
Unparalleled access to key infrastructure hubs, enabling seamless integration with cloud providers, carrier hotels and enterprise facilities.

FAQs
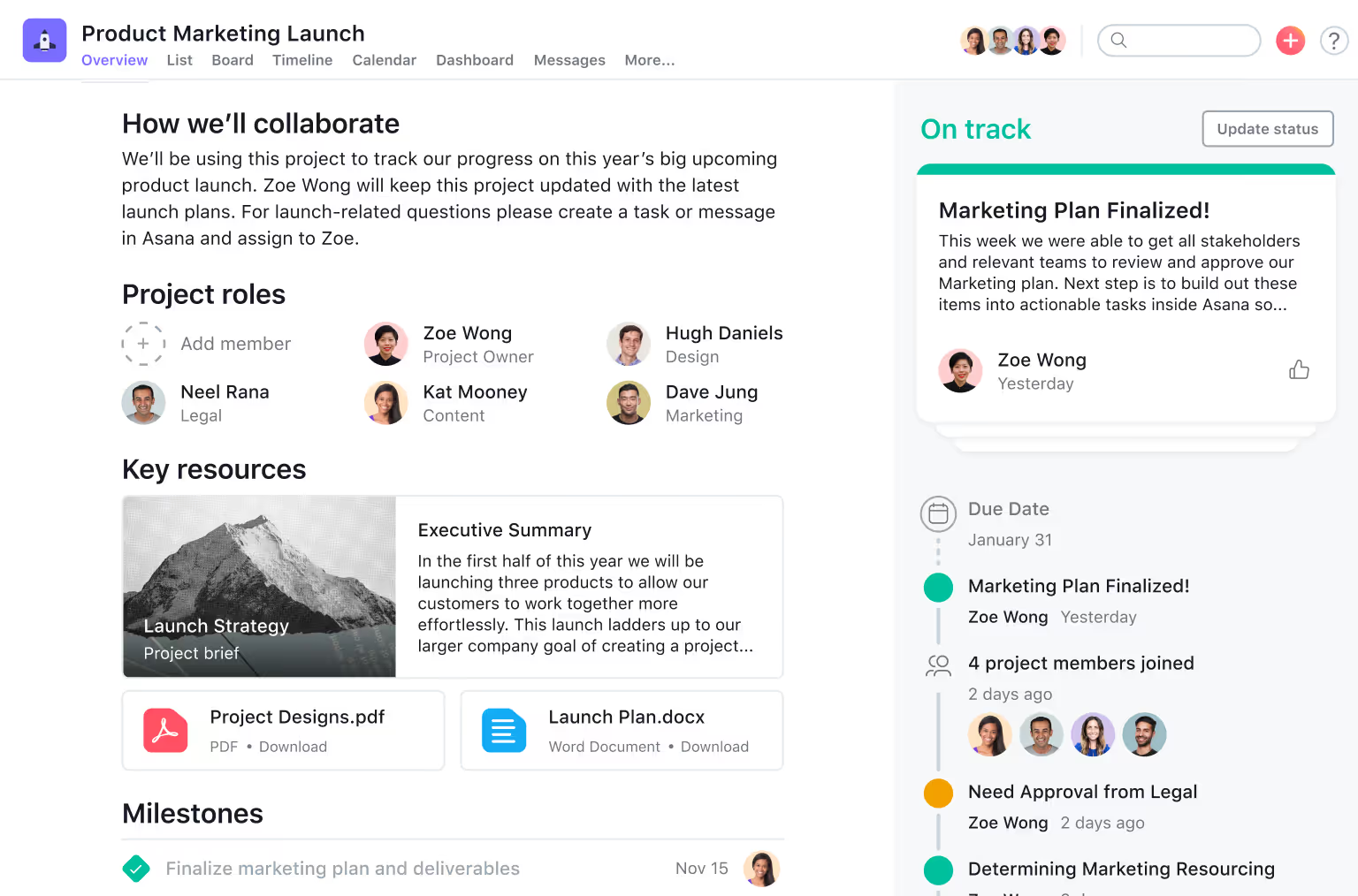
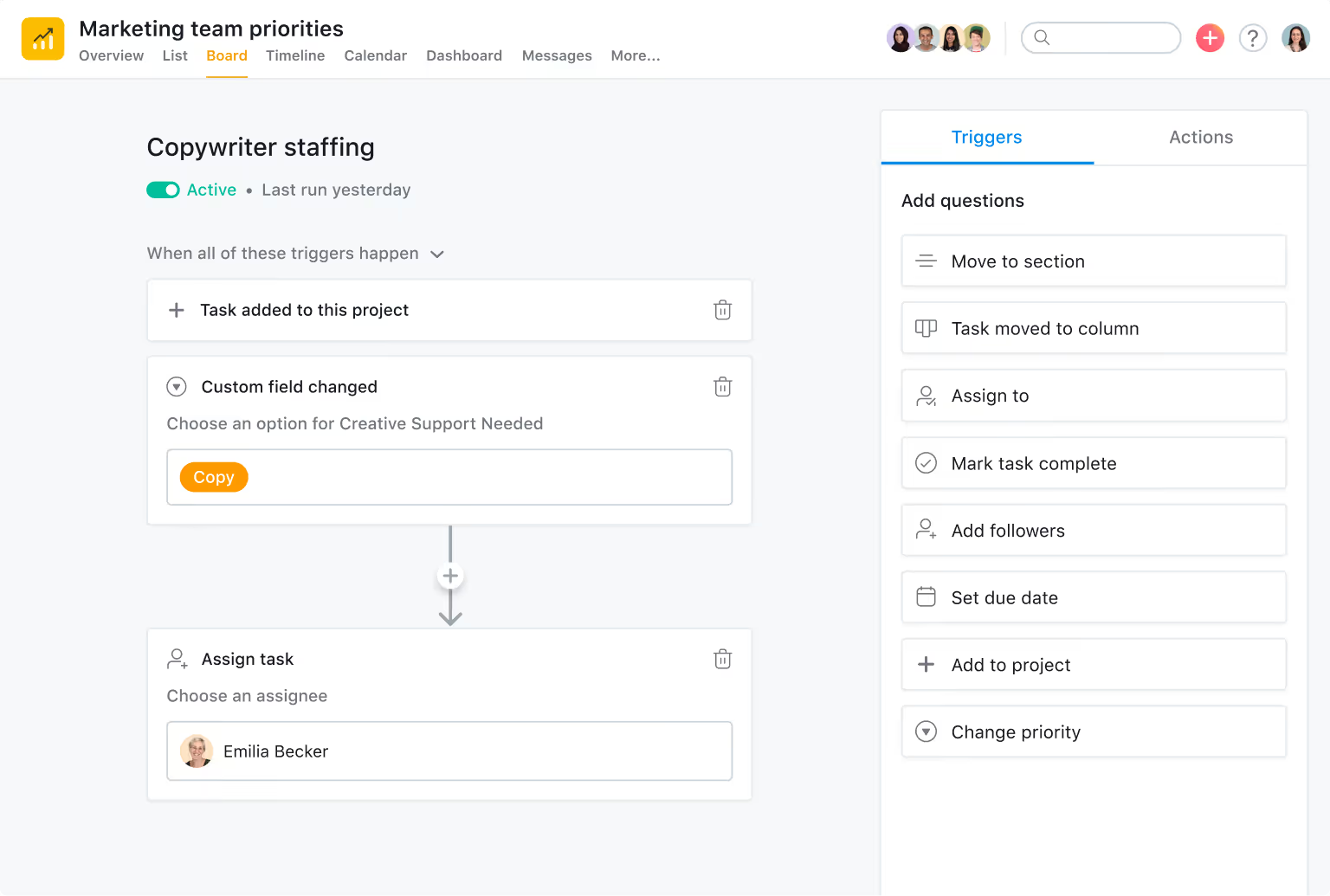
SSE (Security Service Edge) is a powerful, cloud-delivered security solution that brings essential security services together to keep your business safe. It gives remote users secure, seamless access to SaaS, web, and private apps, wherever they are. These integrated services work as one to protect users, devices, and application edges, no matter the location. Features include the latest secuirty technologies such as SWG, CASB, ZTNA, FWaaS, DLP, RBI and DEM all delivered and scaled on demand as our cusotmers require.
In 2022, Gartner introduced Secure Service Edge (SSE) as the security side of SASE. SSE is the cloud-delivered security layer that includes Firewall-as-a-Service (FWaaS), Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), and Zero Trust Network Access (ZTNA), and other serivices like Data Loss Prevention (DLP) and Remote Browser Isolation (RBI). Pair that with a software-defined wide-area network (SD WAN), and you get SASE: SD-WAN + SSE = SASE.
You may also be interested in
The extraordinary everyday.
By tackling the complexities and frustrations of the everyday, we take away the grind - making room for the extraordinary.